A swimming pool full of bitcoins
Buying or selling bitcoin uses 16,000 litres of clean water for every single transaction, which could exacerbate existing droughts around the world.
The majority of the water consumption comes from electricity production, such as in coal and gas plants, or throughput in hydroelectric power stations, says de Vries. He used data on the electricity mix at locations where bitcoin mining occurs to calculate the totals, but also factored in that water is also used directly in data centres to cool the powerful hardware used by miners.
https://www.cell.com/cell-reports-sustainability/fulltext/S2949-7906(23)00004-6
Found here: https://blog.dshr.org/2023/12/why-worry-about-resources.html
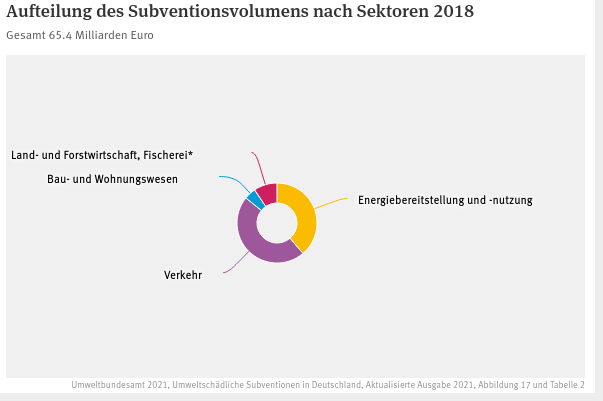
Wenn im Haushalt 60 Mrd. fehlen…
… dann hilft das Umweltbundesamt und listet umweltschädliche Subventionen in Höhe von 65,4 Mrd. Euro auf…
Using Ubuntu as Digital Audio Workstation
Connect an audio interface to your computer.
1. Install kxstudio sources
# Update software sources sudo apt-get update # Install required dependencies if needed sudo apt-get install apt-transport-https gpgv wget # Download package file wget https://launchpad.net/~kxstudio-debian/+archive/kxstudio/+files/kxstudio-repos_11.1.0_all.deb # Install it sudo dpkg -i kxstudio-repos_11.1.0_all.deb
2. Install Cadence
sudo apt-get update sudo apt install cadence
3. Start Cadence and open Catia
Press WIN and search for Cadence. Press Start Button. Open the Tools-Tab and start Catia.
4. Install Reaper
Download from https://www.reaper.fm/download.php
Extract tar.
cd reaper_linux_x86_64 sudo bash install-reaper.sh
5. Start Reaper
Press WIN and search for Reaper.
6. Find Reaper in Catia and look at the wiring. Reaper should be connected to your audio interface.
7. Add a new track to your reaper project.
8. Press the red record item on the track to activate the track for recording
9. Select the proper channel, right below the record button. Connect an audio source, e.g. guitar, microphone, synth to your audio interface. If the correct channel is selected you should see the audio signal on the tracks input meter.
10. Press the record button at the bottom of reaper to record.
OWASP Devsecops Maturity Model
https://owasp.org/www-project-devsecops-maturity-model/
Attackers are intelligent and creative, equipped with new technologies and purpose. Under the guidance of the forward-looking DevSecOps Maturity Model, appropriate principles and measures are at hand implemented which counteract the attacks.
Container Security Verification Standard
https://github.com/OWASP/Container-Security-Verification-Standard
a community-effort to establish a framework of security requirements and controls that focus on normalizing the functional and non-functional security controls required when designing, developing and testing container-based solutions with a focus on Docker.
OWASP Application Security Verification Standard
https://owasp.org/www-project-application-security-verification-standard/
The OWASP Application Security Verification Standard (ASVS) Project provides a basis for testing web application technical security controls and also provides developers with a list of requirements for secure development.
OWASP SAMM
https://owasp.org/www-project-samm/
Our mission is to provide an effective and measurable way for you to analyze and improve your secure development lifecycle. SAMM supports the complete software lifecycle and is technology and process agnostic. We built SAMM to be evolutive and risk-driven in nature, as there is no single recipe that works for all organizations.
Security Code Scan – static code analyzer for .NET
Find Security Bugs
https://find-sec-bugs.github.io/
The SpotBugs plugin for security audits of Java web applications.
Zed Attack Proxy (ZAP)
If you are new to security testing, then ZAP has you very much in mind. Check out our ZAP in Ten video series to learn more!
OWASP Dependency-Check
https://owasp.org/www-project-dependency-check/
Dependency-Check is a Software Composition Analysis (SCA) tool that attempts to detect publicly disclosed vulnerabilities contained within a project’s dependencies. It does this by determining if there is a Common Platform Enumeration (CPE) identifier for a given dependency. If found, it will generate a report linking to the associated CVE entries.
OWASP Proactive Controls
https://owasp.org/www-project-proactive-controls/
The OWASP Top Ten Proactive Controls describes the most important controls and control categories that every architect and developer should absolutely, 100% include in every project.
OWASP Mobile Top 10
Prowler Scanner
Prowler is an Open Source security tool to perform AWS, GCP and Azure security best practices assessments, audits, incident response, continuous monitoring, hardening and forensics readiness.
Testssl
is a free command line tool which checks a server’s service on any port for the support of TLS/SSL ciphers, protocols as well as recent cryptographic flaws and more.
Distroless Container Images
https://github.com/GoogleContainerTools/distroless
Less is more.
“Distroless” images contain only your application and its runtime dependencies. They do not contain package managers, shells or any other programs you would expect to find in a standard Linux distribution.
Semgrep
Semgrep helps security engineers and developers find and fix the issues that matter before production.
php security
https://github.com/FloeDesignTechnologies/phpcs-security-audit
phpcs-security-audit is a set of PHP_CodeSniffer rules that finds vulnerabilities and weaknesses related to security in PHP code.